Vidar Stealer
The Vidar Stealer malware is a classic InfoStealer Trojan that was identified by computer security researchers in December 2018. The Vidar Stealer malware is based on an earlier project called Arkei, but it has notable differences like 'Command and Control' server switches every four days; a new format for the collected information; and a heavily modified grabber component. The Vidar Stealer is offered by its developers using the Malware-as-a-Service (MaaS) business model where third parties pay a lease to use the malware product and earn a profit.
The Vidar Stealer is believed to be operated by Russian-speaking threat actors primarily since most versions of the malware include a blacklist of countries associated with the former Soviet Union. The Vidar Stealer is configured to terminate on computers that are identified to run from Russia (RU), Belarus (BY), Uzbekistan (UZ), Kazakhstan (KZ) and Azerbaijan (AZ). The Vidar Stealer is written in C++ and may appear in the Task Manager of infected hosts as 'vidar.exe.' The Vidar Stealer Trojan is suspected to have been in business since October 2018, and it is sold at a rate of 250-700 USD depending on the subscription plan chosen by the customers. The Vidar Stealer enables the threat actors to collect a wide range of information from compromised systems including:
- Documents and program files in formats like .TXT, .DAT, .AUTH, .UTC, .CRYPT and .KEY.
- Web browser cookies.
- Web browser history and download logs from Google Chrome (and derivatives), Mozilla Firefox (and derivatives), Edge and Internet Explorer, including records in the TOR Browser.
- Web browser auto-fill records like credit cards, home address, phone number and primary email account linked to online payments.
- Offline cryptocurrency wallets.
- Tokens from 2-factor authentication software like Authy from Authy.com.
- Saved messages from Telegram, Steam, Discord, Pidgin, and Skype, as well as email clients like Thunderbird and The Bat!
- Saved login-credentials for FileZilla and WinSCP.
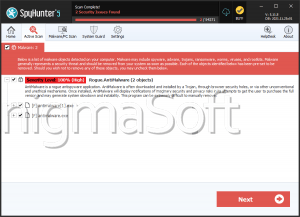
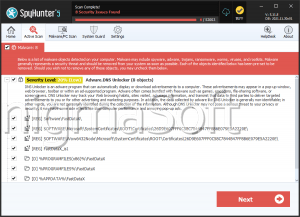
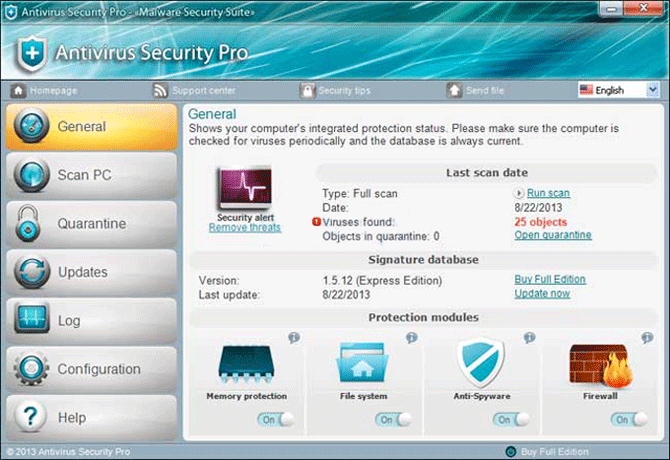
In addition, the Vidar Stealer can take screenshots of the user's desktop and make a list of the installed software along with configuration settings. The Vidar Stealer is promoted to lack dependencies outside its payload, but researchers discovered it downloads DLL libraries associated with the Firefox browser and drops them to the ProgramData directory. The Vidar Stealer is known to extract digital coins from eighteen types of cryptocurrencies, among which are Litecoin, Bitcoin, Ethereum, Zcash and DashCore. The malware is recorded to infect systems via spam emails, pirated software and hack programs for popular PC games. It is a smart idea to use a password manager and avoid software that may come from questionable sources. The Vidar Stealer can be removed with the help of a reputable anti-malware solution.