Xervoo.net
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
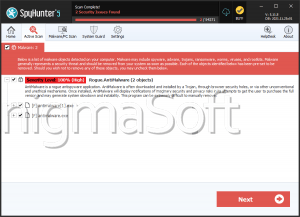
| Ranking: | 2,322 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 155,774 |
| First Seen: | January 25, 2019 |
| Last Seen: | May 24, 2023 |
| OS(es) Affected: | Windows |
Xervoo.net is a rogue website dedicated to the distribution of misleading and deceptive content. Users are not likely to encounter the page or any of the countless other misleading sites that operate in a similar manner intentionally. No, these frauds are predominantly spread vie forced redirects or as a result of the actions of intrusive PUPs (Potentially Unwanted Programs).
After landing on Xervoo.net visitors will be presented with manipulative and misleading messages. Typically, the page would try to create the impression that it is running a CAPTCHA check. Users will be urged to click the shown 'Allow' button supposedly to prove that they are not robots. Other common tactics include promising access to additional content, videos, or files ready to be downloaded. Xervoo.net also has been observed to promise its users a $50 gift card. However, the goal of the hoax website is to get the user to subscribe to its push notifications unknowingly.
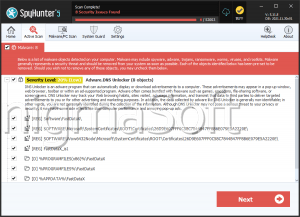
The fraudsters can then proceed to deliver unwanted and annoying advertisements to the user's device. The advertisements should not be trusted. They could be used to promote shady phishing pages, fake giveaways or suspicious adult-oriented websites. Users also could be shown various offers to download dubious applications that could turn out to be adware, browser hijackers or other PUPs.